Most digital marketing teams lose 40 to 70% of their analytics data due to non-compliant implementations, yet many still believe legitimate interest justifies cookie tracking without consent. This misconception creates serious legal risk under regulations like GDPR and CCPA. Privacy compliance isn’t just about avoiding fines; it’s about building accurate measurement systems that respect user rights while delivering actionable insights. This guide clarifies consent models, data recovery techniques, PII prevention strategies, and practical compliance frameworks to help you navigate the complex intersection of analytics and privacy law.
Table of Contents
- Key takeaways
- Understanding privacy regulations and consent models
- Techniques to minimize data loss and improve compliance
- Privacy principles and common pitfalls in analytics data collection
- Navigating consent controversies and building trust with users
- Enhance your analytics compliance with Trackingplan
- FAQ
Key Takeaways
| Point | Details |
|---|---|
| Opt in rules | GDPR requires opt in for non essential analytics cookies and CCPA enables opt out with a GPC signal. |
| Consent Mode recovery | Consent Mode v2 plus server side tracking can recover a substantial portion of analytics data that would be lost without it, reducing data loss from about 40 to 70 percent to roughly 15 to 30 percent. |
| PII masking practices | PII must be detected and masked proactively to prevent exposing personal information in analytics data. |
| Audit and design practices | Regular audits and privacy by design practices minimize regulatory risk and improve data quality. |
Understanding privacy regulations and consent models
Privacy regulations fundamentally reshape how you collect and process analytics data. GDPR requires opt-in consent for non-essential analytics cookies, while CCPA uses an opt-out model honoring Global Privacy Control. This distinction matters because GDPR applies to any organization processing EU resident data, regardless of where your business operates. CCPA covers California residents but has inspired similar laws across multiple US states.
The opt-in versus opt-out difference creates significant operational complexity. Under GDPR, you cannot set analytics cookies until a user actively consents by clicking accept on your banner. CCPA allows you to set cookies by default, but you must immediately stop if a user opts out or their browser sends a GPC signal. Many organizations comply with GDPR globally for simplicity, then geo-target consent experiences to reduce friction in regions with less strict requirements.
Non-compliance carries substantial penalties. GDPR fines reach up to 4% of global annual revenue or €20 million, whichever is higher. CCPA violations cost $2,500 per unintentional breach and $7,500 per intentional violation. Beyond financial penalties, regulatory audits consume significant time and resources. The California Privacy Protection Agency has increased enforcement actions in 2026, making compliance more urgent than ever.
Deceptive consent mechanisms known as dark patterns create additional legal exposure. Regulators scrutinize designs that manipulate users into accepting tracking, such as:
- Pre-checked consent boxes that assume acceptance
- Reject buttons hidden behind multiple clicks while accept is prominent
- Confusing language that obscures what users are consenting to
- Walls that block content access unless users accept all cookies
Pro Tip: Implement a consent management platform that documents user choices with timestamps and consent strings. This audit trail proves compliance if regulators investigate your practices. Consider using marketing data governance frameworks to maintain consistent privacy standards across all data collection activities.
The legal landscape continues evolving. Several US states enacted comprehensive privacy laws in 2024 and 2025, creating a patchwork of requirements. While these laws share common principles with CCPA, nuances in definitions and enforcement create complexity. Most legal experts recommend treating GDPR as your baseline standard because it represents the strictest requirements you’ll encounter.
Techniques to minimize data loss and improve compliance
Consent requirements inevitably reduce the volume of analytics data you collect, but advanced technical implementations dramatically minimize this loss. Implementing cookie consent without Google Consent Mode leads to 40-70% data loss; Consent Mode v2 recovers 15-30%. This technology works by sending privacy-safe pings to analytics platforms even when users decline cookies, allowing statistical modeling to fill gaps in your data.
Consent Mode v2 introduces two critical parameters: ad_storage and analytics_storage. When users decline consent, Google Analytics receives signals about page views and conversions without setting cookies or collecting personal identifiers. The platform then uses machine learning to estimate the behavior of non-consenting users based on patterns from consenting users. This approach maintains reasonable accuracy for aggregate reporting while respecting privacy choices.
Server-side tracking provides even greater data recovery and compliance benefits. Server-side tracking reduces consent-related data loss, blocks ad blockers up to 37% improvement. Unlike client-side tracking where browsers execute JavaScript tags, server-side architectures route data through your own servers before forwarding to analytics platforms. This gives you complete control over what data gets collected, when consent checks occur, and how PII gets filtered.
![]()
| Implementation approach | Data retention rate | Compliance risk | Setup complexity |
|---|---|---|---|
| No consent management | 100% | Critical | Low |
| Basic consent banner | 30-60% | Medium | Low |
| Consent Mode v2 | 45-75% | Low | Medium |
| Server-side + Consent Mode | 70-90% | Very low | High |
Integrating your consent management platform with your tag management system creates seamless consent enforcement. Modern CMPs like OneTrust, Cookiebot, and Usercentrics offer native integrations with Google Tag Manager, Adobe Launch, and Tealium. These integrations automatically suppress tags when users decline consent categories, eliminating the risk of accidental non-compliant tracking.
Practical implementation requires several technical steps:
- Configure your CMP to define consent categories aligned with cookie purposes
- Map each tag in your TMS to appropriate consent categories
- Implement Consent Mode v2 parameters in your analytics tags
- Set up server-side tracking endpoints if pursuing advanced data recovery
- Test consent flows across devices and browsers to verify proper suppression
Pro Tip: Audit your analytics implementation monthly using server side tracking validation tools. Check that tags fire only after appropriate consent, verify no PII leaks into analytics properties, and confirm consent choices persist correctly across sessions. Regular monitoring helps you catch configuration errors before they create compliance issues. Learn more about systematic approaches in guides on how to prevent data loss.
The technical investment in privacy-compliant analytics pays dividends beyond avoiding fines. Cleaner data collection reduces noise from bot traffic and invalid interactions. Server-side architectures improve page load performance by reducing client-side JavaScript execution. Most importantly, transparent consent practices build user trust, which correlates with higher engagement and conversion rates over time.
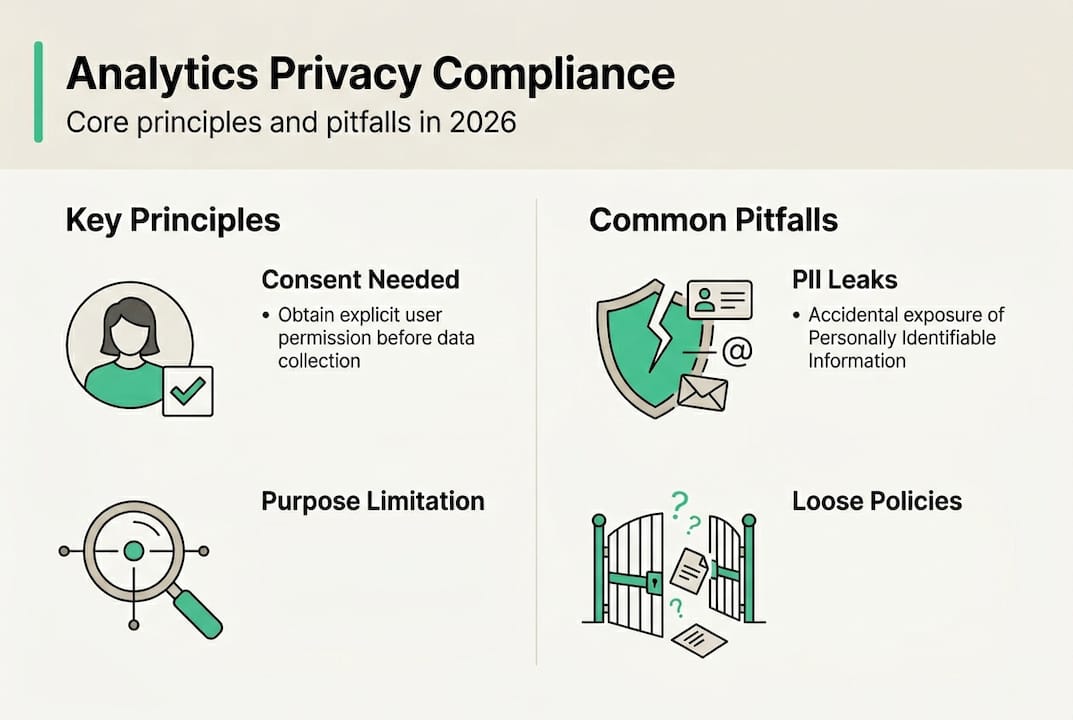
Privacy principles and common pitfalls in analytics data collection
Effective privacy compliance rests on foundational principles that extend beyond consent mechanics. Core privacy principles for analytics: data minimization, purpose limitation, PII detection/prevention, hashing/pseudonymization. Data minimization means collecting only information necessary for specific business purposes. Purpose limitation requires using collected data exclusively for stated purposes, not repurposing it later for unrelated activities.
Personally identifiable information creates the highest compliance risk in analytics implementations. PII includes obvious identifiers like names, email addresses, and phone numbers, but also encompasses IP addresses, device IDs, and any data that could identify individuals when combined. Edge cases include PII leaks in URL parameters and custom events; CIPA requires blocking contents capture without consent. Common leak vectors include:
- URL parameters containing user IDs, email addresses, or session tokens
- Form field values captured in custom events before submission
- Search terms that reveal sensitive personal information
- Referrer headers exposing data from authenticated pages
- Custom dimensions populated with customer names or account numbers
The California Invasion of Privacy Act introduces unique requirements for content capture technologies. CIPA mandates that businesses obtain explicit consent before recording keystrokes, mouse movements, or session replays. This affects popular analytics tools like Hotjar, FullStory, and Clarity. You must present clear consent requests specifically for session recording, separate from general analytics consent.
Many compliance breaches occur from tags firing before consent resolution. If your analytics tags load synchronously in the page head, they may execute before your consent banner appears and captures user choice. This creates a window where non-compliant tracking occurs for every visitor. The solution involves:
- Loading your CMP script first with highest priority
- Blocking all analytics tags until consent state resolves
- Using consent callbacks to trigger tag execution only after user choice
- Implementing default deny states for all consent categories
Automating PII detection prevents manual oversight errors. Modern data governance platforms scan your analytics data streams in real time, flagging potential PII using pattern matching and machine learning. When PII is detected, automated masking rules can hash, pseudonymize, or redact the sensitive data before it reaches analytics platforms. This approach scales far better than manual reviews as your tracking implementation grows.
| PII type | Common location | Detection method | Remediation |
|---|---|---|---|
| Email addresses | URL parameters, form events | Regex pattern matching | Hash or remove |
| Phone numbers | Custom dimensions | Format validation | Mask digits |
| Names | Event properties | NLP entity recognition | Pseudonymize |
| IP addresses | Automatic collection | Default analytics capture | Anonymize or truncate |
Pro Tip: Create a PII detection checklist specific to your analytics implementation. Document every custom event, dimension, and parameter you collect. Review each for PII risk and implement appropriate safeguards. Resources like what is pii and pii data compliance provide detailed frameworks for this process.
Purpose limitation affects how you can use analytics data downstream. If you collect data with consent for website optimization, you cannot later use that same data for email marketing without obtaining separate consent. This principle requires careful data governance documentation. Maintain clear records of what consent covers which data uses, and enforce technical controls that prevent unauthorized data sharing between systems.
Navigating consent controversies and building trust with users
The legitimate interest versus consent debate continues generating confusion among marketers. Most regulators reject legitimate interest for analytics cookies; consent is required for non-essential processing. While GDPR technically allows legitimate interest as a legal basis for processing, European data protection authorities consistently rule that analytics tracking fails the legitimate interest test. The reasoning centers on user expectations and the availability of less intrusive alternatives.
Legitimate interest requires a three-part assessment: necessity test, balancing test, and safeguards evaluation. For analytics, the necessity test asks whether tracking is essential for your business operations. Since businesses operated successfully before digital analytics existed, regulators argue tracking is not strictly necessary. The balancing test weighs your interests against user privacy rights. Given that users increasingly expect privacy and control, their rights typically outweigh business interests in behavioral tracking.
Some organizations attempt to use legitimate interest for first-party analytics while requiring consent for third-party advertising cookies. This approach carries significant risk. The UK Information Commissioner’s Office, French CNIL, and other authorities have issued guidance explicitly stating that legitimate interest rarely applies to analytics cookies. Several high-profile enforcement actions have resulted in substantial fines for organizations that relied on this interpretation.
Securing explicit consent remains the safest compliance strategy:
- Present clear, plain language explanations of what data you collect
- Separate consent requests for different processing purposes
- Make acceptance and rejection equally easy for users
- Allow granular consent choices rather than all-or-nothing options
- Provide simple mechanisms to withdraw consent at any time
Privacy-by-design principles offer the most robust long-term compliance framework. This approach embeds privacy considerations into every stage of product development and data collection. Rather than bolting on consent banners as an afterthought, privacy-by-design means architecting systems that minimize data collection, encrypt sensitive information, and provide transparency by default.
Privacy is not just about compliance. It’s about building sustainable relationships with customers based on respect and transparency. Organizations that treat privacy as a competitive advantage rather than a burden consistently outperform peers in customer trust metrics.
The economic case for privacy compliance extends beyond avoiding penalties. Compliance costs are high initially but net positive because 81% of consumers avoid firms they don’t trust. This trust deficit directly impacts conversion rates, customer lifetime value, and brand reputation. Conversely, companies known for strong privacy practices enjoy premium positioning and customer loyalty.
Regular compliance audits should become standard practice. Quarterly reviews of your consent implementation, PII handling, and data governance documentation help catch issues before they escalate. These audits should examine:
- Consent banner language and user experience flows
- Tag firing behavior across consent states
- Data retention policies and deletion procedures
- Vendor contracts and data processing agreements
- Training and awareness among teams handling customer data
Pro Tip: Use a website audit checklist to systematically review privacy and compliance elements. Document findings and remediation timelines. This creates an audit trail demonstrating good faith compliance efforts, which regulators consider during enforcement decisions.
Transparent communication about privacy practices builds user confidence. Rather than hiding your data collection in dense legal policies, explain in simple terms what you track, why it helps improve user experience, and how users can control their data. Some organizations publish privacy dashboards where users can view exactly what data has been collected about them and delete it with one click. This level of transparency differentiates your brand and reduces regulatory scrutiny.
Enhance your analytics compliance with Trackingplan
Navigating privacy compliance while maintaining data quality requires sophisticated monitoring and validation tools. Trackingplan provides automated analytics auditing that detects compliance issues before they create legal exposure. The platform continuously monitors your tracking implementation, flagging PII leaks, consent violations, and configuration errors in real time. This proactive approach prevents the data quality degradation that typically accompanies consent implementations.
![]()
The AI assisted debugger analyzes your analytics data streams to identify anomalies and suggest fixes. When consent changes cause unexpected data loss, the debugger pinpoints exactly which tags are affected and recommends configuration adjustments. Integration with leading digital analytics tools means you can monitor Google Analytics, Adobe Analytics, Mixpanel, and dozens of other platforms from a single dashboard. For comprehensive privacy guidance and compliance resources, explore the Privacy Hub, which offers templates, checklists, and best practices tailored to modern analytics implementations.
FAQ
What is privacy compliance for analytics?
Privacy compliance for analytics means ensuring your data collection practices respect regulations like GDPR and CCPA, particularly regarding user consent and data protection. It includes managing cookies appropriately, preventing PII leaks, and implementing clear consent mechanisms. Compliance requires both legal understanding and technical implementation to balance measurement needs with privacy rights.
How does GDPR consent differ from CCPA consent for analytics?
GDPR requires affirmative opt-in consent before setting non-essential analytics cookies, meaning users must actively accept tracking. CCPA allows an opt-out model where cookies can be set by default, but you must immediately stop tracking when users opt out or their browser sends a Global Privacy Control signal. This fundamental difference affects how you design consent experiences and technical implementations.
What is Consent Mode v2 and why is it important?
Consent Mode v2 is an advanced Google technology that allows analytics platforms to receive privacy-safe signals even when users decline cookies, enabling statistical modeling to estimate non-consenting user behavior. It reduces data loss significantly, recovering 15-30% of analytics data compared to basic consent implementations while fully respecting user privacy choices. The technology maintains aggregate reporting accuracy without compromising individual privacy.
How can marketers detect and prevent PII leaks in analytics?
Use automated PII detection tools that scan your data streams in real time for patterns matching personal information like email addresses, phone numbers, and names. Conduct regular tag audits to verify no sensitive data flows into analytics properties through URL parameters, custom events, or form captures. Implement masking or pseudonymization rules that automatically redact PII before transmission. Learn more about identification and protection strategies at what is pii.
Why is privacy-by-design crucial for compliance and trust?
Privacy-by-design embeds data protection into every stage of system development rather than adding it as an afterthought, minimizing collection and risk from the start. This approach prevents compliance issues before they occur and demonstrates genuine commitment to user privacy. It builds user trust by showing respect for privacy rights, which translates to higher engagement, better conversion rates, and reduced legal exposure over time.