TL;DR:
- Half of all consent management platforms failed in 2024 audits due to inadequate withdrawal clarity and user interface issues. Effective compliance requires technical proof that consent signals are enforced at the network level, not just banner presence, through network logs, auditable records, and continuous monitoring. Ongoing verification and region-specific configurations are essential to ensure regulatory compliance and prevent enforcement actions.
Half of all consent management platforms audited in 2024 failed on withdrawal clarity, and 42% failed on the user interface for withdrawal itself. That number should stop you cold, because it means that most organizations running a CMP believe they are compliant while regulators see something entirely different. Consent enforcement verification is not about whether your banner appears or whether users click “Accept.” It is about whether your technical stack actually blocks data collection when users say no, and whether you can prove it. This article walks through the methodologies, common pitfalls, advanced testing protocols, and regional nuances that separate organizations that pass audits from those that receive enforcement notices.
Table of Contents
- Why consent enforcement verification is critical
- Core methodologies for consent enforcement verification
- Real-world pitfalls and edge cases
- Testing protocols and continuous verification in practice
- Navigating global enforcement standards: US vs. EU, and Google’s new rules
- The uncomfortable truth about consent enforcement: technology gaps and what actually works
- Get continuous, audit-ready consent enforcement with Trackingplan
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Proof over display | Regulators require technical evidence of enforcement, not just visible consent banners. |
| Continuous verification | Automated, routine audits and logged testing are essential to maintain compliance year-round. |
| Pitfalls persist | Even leading CMPs and teams make mistakes with tag loading, GPC signals, and global opt-out propagation. |
| Region-specific nuances | US and EU have fundamentally different consent obligations, and global tools must adapt accordingly. |
| Choose real enforcement | Platforms that provide network log capture, script blocking, and audit exports far outperform visual-only solutions. |
Why consent enforcement verification is critical
Regulators have shifted their expectations dramatically. Showing a consent banner is no longer sufficient evidence of compliance. Authorities across the EU and US now demand technical proof that consent signals are actually enforced at the network level, meaning that tracking calls stop firing when a user opts out or withdraws consent. This is a fundamentally different standard than what most teams were building toward just two years ago.
The numbers paint a stark picture. IAB TCF 2024 audits revealed that 50% of CMPs failed on withdrawal information clarity, and 42% failed on the UI for withdrawal. By 2025, vendor enforcement procedures had doubled to 587 active procedures, with 41 suspensions issued. These are not small operators. These are established platforms with dedicated compliance teams, and they are still failing.
The business risk is real and measurable. Non-compliance does not just mean regulatory fines, though those are significant. It means potential suspension from ad networks, loss of access to Google’s modeling features, and the kind of public enforcement notices that damage brand trust. Understanding consent management fundamentals is the starting point, but verification is where compliance actually lives.
A key concept emerging from recent regulatory guidance is “enforcement evidence.” This means that actual enforcement must be proven through network evidence, auditable logs, and testing mechanisms, not just through the presence of a consent collection interface. Regulators want to see that when a user opts out, the signal travels through your entire stack and stops data from flowing. Reviewing top CMP solutions can help you identify platforms built with this level of technical enforcement in mind.
Here is what enforcement evidence means in practice:
- Network request logs showing no ad or analytics calls after opt-out
- Timestamped audit records tied to specific user sessions
- Tag suppression confirmation from your tag manager
- Cross-device opt-out records showing persistence beyond a single session
- Regulatory-ready exports formatted for GDPR Article 7 requirements
“The question regulators are asking is no longer ‘do you collect consent?’ It is ‘can you prove that consent decisions are technically enforced across every touchpoint in your stack?’”
Core methodologies for consent enforcement verification
Now that we know why verification matters, let us break down the essential methodologies and practical tools that enable reliable consent enforcement validation.
The foundation of any verification program is network log comparison. This involves capturing all outbound network requests before and after a consent decision, then comparing them to confirm that restricted calls stop firing when consent is denied. This is not a manual process you can run once a quarter. It needs to be systematic, repeatable, and documented.

Tamper-proof logging with timestamps, user agent data, banner snapshots, and immutable audit trails forms the backbone of defensible compliance. Blockchain-backed audit trails are increasingly being used by enterprise teams because they provide cryptographic proof that records have not been altered after the fact. For GDPR Article 7 purposes, this level of immutability is becoming a practical necessity rather than a premium feature.
Here is a comparison of traditional versus advanced enforcement evidence approaches:
| Verification approach | Traditional method | Advanced enforcement evidence |
|---|---|---|
| Consent record storage | Database log with timestamp | Immutable/blockchain-backed audit trail |
| Network verification | Manual spot-check | Automated pre/post opt-out capture |
| User agent tracking | Not collected | Stored with each consent event |
| Banner documentation | Screenshot on request | Automated snapshot at each interaction |
| Cross-device sync | Not verified | Active session reconciliation |
| Regulatory export | Manual CSV export | Structured GDPR Article 7 export |
| Audit frequency | Annual review | Continuous automated monitoring |
The numbered steps for building a core verification methodology are:
- Establish a baseline network log by capturing all requests on a clean session before any consent interaction.
- Trigger a consent denial or opt-out and immediately capture the resulting network activity.
- Compare the two logs to identify any calls that should have stopped but did not.
- Store the comparison output with a timestamp, user agent string, and a screenshot of the consent UI at the time of the interaction.
- Export the records in a format that satisfies GDPR Article 7 or CCPA audit requirements.
- Schedule repeat runs on a defined cadence, especially after any tag manager or CMP configuration change.
You can deepen this process by learning how to audit Consent Mode v2 specifically, since Google’s implementation introduces its own verification requirements. For a broader framework, the privacy compliance guide for analytics covers the full landscape of what modern stacks need to address.
Pro Tip: Store your consent evidence in a separate, access-controlled environment from your main analytics data. If your analytics database is ever questioned in an audit, you want your compliance records to be independently verifiable and clearly segregated.
Real-world pitfalls and edge cases
Even with solid methodology, real-world platforms introduce technical snags and compliance blind spots. This is where mature stacks often get caught off guard, because the failure modes are subtle and easy to miss in routine testing.
The most common and damaging issue is pre-consent pixel firing. This happens when a tag fires before the CMP has resolved the user’s consent status. In practice, pixels fire before CMP resolution because of asynchronous tag loading, where the tag manager executes before the CMP script has finished loading and communicated the consent state. The result is that tracking data is collected in a window that regulators consider a clear violation, even if the user ultimately denies consent a second later.
GPC (Global Privacy Control) signal handling is another persistent weak spot. Many stacks detect the GPC browser signal but fail to propagate it correctly to tag managers, CDPs, and downstream vendors. Account-level opt-out also frequently fails to sync across devices and sessions, meaning a user who opts out on mobile may still be tracked on desktop. These are not edge cases in the theoretical sense. They are common failure patterns across real production environments.
Here are the most frequent technical pitfalls to stress-test in your own setup:
- Async tag race conditions: Tags loading and firing before the CMP resolves consent status
- GPC propagation failures: Signal detected at the browser but not passed to GTM, CDPs, or server-side systems
- Session persistence gaps: Opt-out not carrying forward across new sessions or browser restarts
- Cross-device sync failures: Consent state not reconciled between mobile and desktop for logged-in users
- Vendor list lag: New vendors added to your stack not yet included in your CMP’s blocking rules
- Partial consent handling: Tags that fire for some purposes but not others, creating ambiguous data collection states
“The most dangerous compliance gap is not the one you know about. It is the tag that fires silently in a race condition window before your CMP has even rendered.”
Testing for these issues requires deliberate scenario construction. You need to simulate slow network conditions to expose race conditions, test with GPC enabled across multiple browsers, and verify opt-out persistence by clearing sessions manually and checking whether consent state is correctly restored. The guide on how to prevent tags firing before consent provides a structured approach to catching these issues before auditors do. The consent and cookies checker tool can also help you identify which cookies and scripts are active before a consent decision is made.
Pro Tip: Run your consent audit scripts on a scheduled basis after every deployment, not just after major releases. Configuration drift in tag managers is one of the leading causes of silent compliance failures, and it often happens through small, incremental changes that individually seem harmless.
Testing protocols and continuous verification in practice
With the pitfalls in mind, here is how to establish airtight, proactive consent enforcement verification through codified test protocols and ongoing monitoring.
The core principle is that consent verification cannot be a point-in-time activity. Regulatory guidance increasingly reflects this. Consent validity requires granular purposes, equal prominence for reject and accept options, easy withdrawal, and periodic refresh. Each of these requirements has a technical testing analog that should be part of your regular protocol.
Here is a structured testing protocol you can implement immediately:
- Capture baseline network requests using browser developer tools or a proxy tool like Charles or Fiddler on a fresh, cookie-free session.
- Deny all consent at the CMP banner and capture the resulting network activity within a 30-second window.
- Verify that no ad network calls, analytics hits, or pixel fires appear in the post-denial capture. Any call that appears is a violation candidate.
- Enable GPC in your browser and reload the page without interacting with the banner. Verify that the CMP automatically suppresses tracking without requiring user interaction.
- Check GTM’s tag firing behavior by reviewing the GTM preview mode to confirm that consent-gated tags show as “not fired” when consent is denied.
- Test cross-device persistence by opting out on one device, then logging into the same account on a second device and verifying that the opt-out state is recognized.
- Document all results with timestamps, screenshots, and network log exports stored in your compliance evidence repository.
The following table maps test scenarios to the evidence types they generate:
| Test scenario | Evidence captured | Regulatory relevance |
|---|---|---|
| Pre-consent network capture | Baseline request log | GDPR Article 7, CCPA |
| Post-denial network capture | Suppression confirmation | GDPR, CCPA, TCF |
| GPC signal test | Auto-suppression log | CCPA/CPRA 2026 |
| GTM tag suppression check | Preview mode screenshot | Internal audit |
| Cross-device opt-out test | Session reconciliation log | GDPR, CCPA |
| Withdrawal UI test | Banner screenshot + timestamp | TCF compliance |
For compliance testing around cookies, the key is verifying not just that cookies are blocked but that the blocking persists correctly across the full session lifecycle. Integrating your CMP with data quality monitoring tools enables continuous, automated verification rather than relying on manual test runs.
Testing protocols should include capturing network logs before and after opt-out, verifying no ad network calls with GPC enabled, checking tag suppression in GTM, and confirming cross-device opt-out persistence. These are not optional steps. They are the minimum required to generate the enforcement evidence that regulators expect to see.
Pro Tip: Automate your consent test suite using a headless browser framework like Playwright or Puppeteer. You can schedule these tests to run nightly and alert your team via Slack or email when any test fails, giving you near-real-time detection of compliance drift without manual effort.
Navigating global enforcement standards: US vs. EU, and Google’s new rules
With verification frameworks in place, it is time to operationalize compliance globally and understand the region-specific and vendor-specific nuances that will determine whether your program holds up under scrutiny.
The fundamental difference between US and EU frameworks is the direction of consent. GDPR requires opt-in prior blocking, meaning no tracking occurs until the user actively consents. CCPA and CPRA operate on an opt-out model, where tracking is permitted by default unless the user signals otherwise. However, CCPA/CPRA opt-out requirements are tightening significantly, with GPC signal detection becoming mandatory and visible opt-out confirmation required from 2026 onward. CMPs must now handle region-specific logic, including automatically suppressing banners and tracking when a GPC signal is detected from a California user.
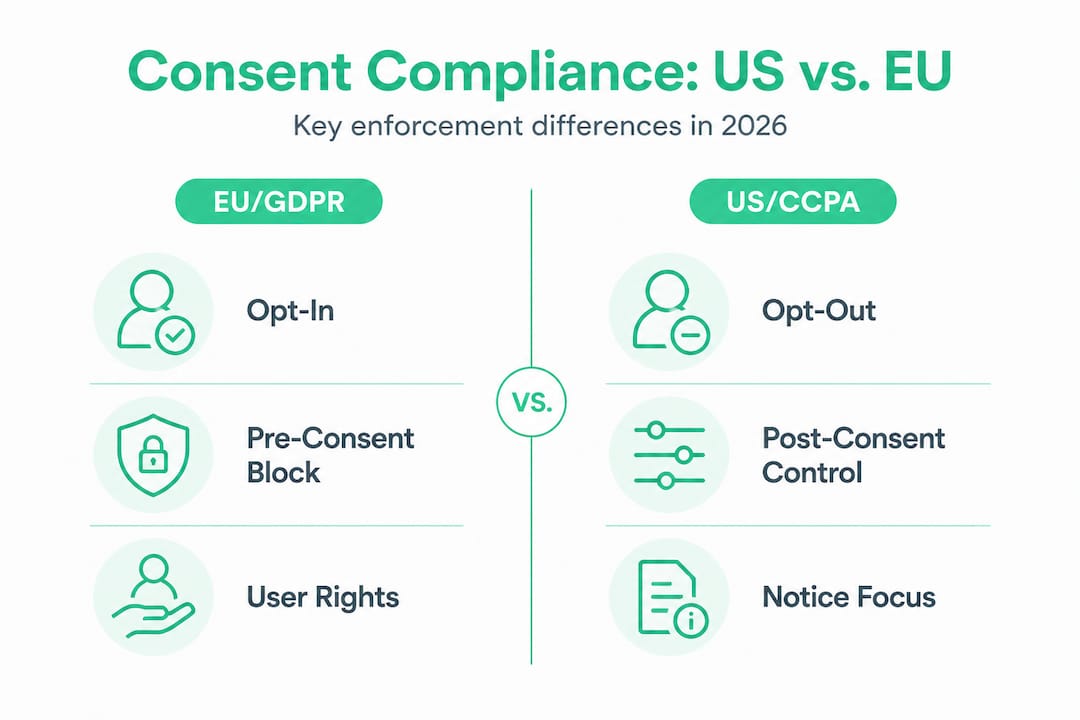
Here is a comparison of the key regulatory and technical requirements by region and platform:
| Requirement | GDPR (EU/EEA) | CCPA/CPRA (US/CA) | Google Consent Mode v2 |
|---|---|---|---|
| Default state | Denied (opt-in required) | Permitted (opt-out model) | Default denied for EEA/UK |
| GPC signal | Recognized, not mandated | Mandatory detection | Must be handled |
| Banner requirement | Required before tracking | “Do Not Sell” link required | CMP integration required |
| Granular purposes | Required | Category-level | 4 specific parameters |
| Withdrawal mechanism | Must be as easy as consent | Must be accessible | Not applicable |
| Audit trail | GDPR Article 7 | Reasonable records | Google-specific logs |
The Google Consent Mode v2 situation deserves special attention. Non-compliant EEA and UK sites saw 90 to 95% drops in measurable analytics and ad metrics when enforcement kicked in. The correct implementation requires setting the default state to “denied” for all four parameters (ad_storage, analytics_storage, ad_user_data, and ad_personalization), using wait_for_update to prevent race conditions, and ensuring your CMP updates these parameters correctly based on user choice.
Key points to verify in your Google Consent Mode v2 setup:
- Default denied state configured before any tags fire
- wait_for_update parameter set to give the CMP time to resolve consent before tags execute
- All four consent parameters explicitly addressed in your CMP configuration
- Consent Mode integration verified through Google Tag Assistant or a dedicated audit
- Modeled data behavior understood and documented for reporting purposes
For a deep technical walkthrough, the guide on how to audit for Consent Mode v2 covers the specific checks needed to confirm correct implementation. If you are also running Microsoft advertising, the Microsoft Consent Mode guide addresses the parallel requirements for that platform.
Regional tailoring is not optional. A CMP configured for GDPR will not automatically satisfy CCPA requirements, and a setup optimized for US traffic may actively violate EU rules if applied globally without region detection logic. Your CMP must be capable of detecting user location and applying the appropriate consent framework dynamically.
The uncomfortable truth about consent enforcement: technology gaps and what actually works
Here is the pattern we see repeatedly: a team invests in a reputable CMP, configures it carefully, runs a few manual tests, and then considers consent compliance handled. Then an audit happens, or a regulator sends a letter, and suddenly the gaps are visible. 70% of tracking setups have active violations, with Google Analytics hits firing before consent being one of the most common. The CMP was present. The banner was showing. But enforcement was not actually happening at the network level.
The root cause is almost always the same: teams treat CMP selection as the end of the compliance journey rather than the beginning. They evaluate CMPs on UI quality, ease of configuration, and banner design. These things matter, but they are not what determines whether you pass an audit. What matters is whether the CMP technically blocks network requests, whether it propagates signals to every downstream system, and whether it generates the kind of auditable evidence that regulators accept as proof.
CMPs alone are insufficient without continuous monitoring layered on top. This is not a criticism of CMP vendors. It reflects the reality that your stack is dynamic. Tags get added, configurations change, third-party scripts load in unexpected order, and consent signals get lost in the complexity. No CMP can monitor itself across all these dimensions simultaneously.
What actually works is a multi-layered approach. You need client-side verification (checking what fires in the browser), server-side verification (confirming what reaches your data endpoints), and network-level verification (capturing raw request logs that show the ground truth). Each layer catches different failure modes. Relying on any single layer creates blind spots that auditors will find even if you do not.
The teams that consistently pass audits share a few characteristics. They run automated scans on a regular schedule, not just after major releases. They treat consent evidence as a data product in its own right, with the same quality standards they apply to their analytics data. And they use monitoring tools that operate independently of their CMP, so they get an objective view of what is actually happening in their stack. Reviewing the landscape of choosing the right CMP with these criteria in mind will help you make a selection that supports real enforcement rather than just compliance theater.
The uncomfortable truth is that consent enforcement verification is an ongoing operational discipline, not a configuration task. The organizations that treat it as the latter are the ones generating the failure statistics we cited at the start of this article.
Get continuous, audit-ready consent enforcement with Trackingplan
Consent enforcement verification is only as strong as your ability to monitor it continuously and generate evidence on demand. Manual audits and periodic reviews leave gaps that regulators and automated enforcement systems are increasingly equipped to find.
![]()
Trackingplan provides automated monitoring across your entire analytics and marketing stack, detecting consent enforcement failures in real time and generating the audit-ready evidence your compliance program needs. From pixel monitoring and tag suppression verification to privacy compliance checks and schema auditing, Trackingplan operates as a continuous verification layer that works alongside your CMP rather than depending on it. Explore how analytics tool integrations connect your full stack to a single compliance view, visit the privacy compliance hub for resources tailored to your regulatory environment, and see exactly how Trackingplan works to keep your consent enforcement audit-ready year-round.
Frequently asked questions
What evidence is required to prove consent enforcement for audits?
Regulators look for network evidence, auditable logs, banner snapshots, and immutable audit trails proving actual enforcement through technical mechanisms, not just the presence of a consent collection interface.
How often should consent audits and verifications be performed?
Best practice is to conduct scheduled recertifications every 6 to 12 months and automated scans at least monthly, since periodic refresh and ongoing validity checks are required under GDPR consent standards.
What are common technical gaps in consent enforcement?
Frequent issues include pixels firing before CMP resolution, GPC signal failures to propagate to tag managers and CDPs, and opt-out states not persisting across devices or sessions.
What happens if Google Consent Mode v2 isn’t set up properly?
Non-compliance can cause a 90 to 95% drop in measurable analytics and ad data from EEA and UK users, making accurate attribution and campaign optimization effectively impossible.